In my first write up on the Sophos XG Firewall, I covered my basic network setup and the configuration that I used. Now that I have had a chance to learn it better and do a bit of experimenting, I want to focus more on rules, Web Filtering, Application Filtering, Dynamic DNS, and other features that I configured. I have spent quite a bit of time with it since its release and have become a big fan. As with any of these type of products, there is a learning curve and you have to be willing to invest a bit of time in tweaking things, but once you are done, you will find the results to be excellent.
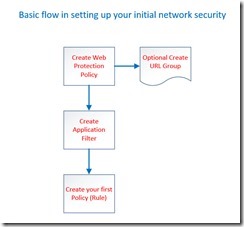
This is the process flow that I used (after a bit of experimenting) to create some powerful home security.
Web Protection
There are many places you can start when creating your network security in Sophos XG, and there is no set way to do it. This is the process I used in building the layer of protection I wanted on my network. One of the first things I did was to begin to build a web filter policy. A web policy is an aggregation of “items” that you can assimilate together and later assign to a “Policy (Rule)” which will be better explained later on.
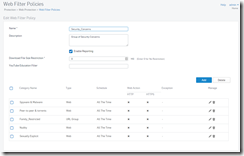
Web Filter policies
In the web filter policies (Protection > Web Protection > Web Filter Policies) you will see many pre made policies that can be used to create rules, however it is much more powerful and easier to understand if you create your own. In the example below you see that I aggregated many categories such as peer to peer & torrents with a custom URL group which I tracked over time by reviewing traffic logs. If I saw a site that show up frequently, I research it and added it to the URL group if I thought it might pose a problem. The point here is that I can add many categories into one custom Web filter policies. To create one, just click ADD, name it, then click the ADD button to begin to add the elements of your policy (in my example, I called it Security_Concerns). You can select Web Category, File Type, or URL group to add. Make sure you select “DENY”, and add as many as you need. I suggest you start with only one or two and test things out to make it easier to troubleshoot should the need arise as it is very easy to edit and add items to later. Once you save this it will be used later when creating your first rule.
URL Groups
As mentioned above, this an aggregation of URLs that I manually put in to supplement the categories. Make sure you know what you are putting in here so that you do not accidently block things you do not want to block.
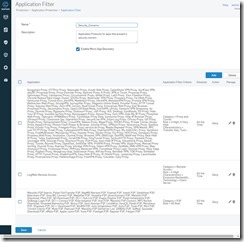
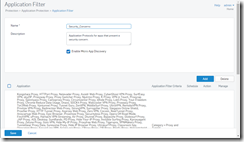
Application Filters
The next area that I focused on was on “Application Filters”. Again this is created so that it can later be added to a Policy (Rule) as part of your overall network security. This is a very powerful section but I found it to be a bit buggy to navigate so I would suggest creating separate sections like I did below. I created each section, saved it, then added more, saved it, etc. This is one of the only areas I found in the software where navigation is a bit temperamental.
Go to the Application Filter Section (Protection > Application Protection > Application Filter) and add a new application filter (in my example I also called this Security_Concerns). Your best bet is to select one category at a time and add it. I found it works best if you refine your search and select the entire category rather than attempting to add/remove individual applications. Remember after you select what you want, select deny, then save it. Add the next section and repeat as many times as needed but remember it is best to start with just a few. The process is similar to Web Policies, just give it a name, check the “Enable Micro App Discovery” box and click the ADD button to begin to add sections.
Making the first Policy (Rule)
This is where the fun starts. Before you get to far, we need to test what we have done by creating our first Policy (Rule). This is where we tie everything together and test it to make sure all is working well. At a minimum, I would test basic connectivity to the internet, critical sites such as banks sites, internal resources such as NAS units, printers, etc. Remember that your IOS/Android devices will be need be bypassed if they are connected directly to Sophos XG or you will need to bypass an access point that will take care of the web filtering.
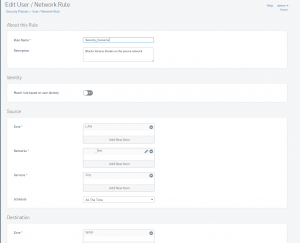
Create a new user/network rule (Security Policies > User / Network Rule). I called mine “Security_Concerns” but use whatever make sense to you. Create the rule as follows:
Source
Zone – LAN (Traffic from your local network)
Network – Here you can select “ANY” or you can use a specific IP, Range of IP’s, Port, or a specific network. In my case, I used this rule only on my secondary network so I specified that. Again you have to decide what you are trying to protect. Selecting “Any” will protect everything on all networks.
Services – Any
Destination
Zone – WAN
Network – Any
Routing
Rewrite Source – On
Use Outbound Address – MASQ
Malware Scanning
Scan HTTPS – Off (Optional, you can enable this if want to try it)
Scan HTTP – On
Application Control – Enter/Select the name of the Application Filter you created in the earlier step. In my case I had also called this “Security_Concerns”.
Web Filtering – Again, select/enter the name of the Web Filter Policy you created in an earlier step when you created a “Web Filter”. In my case it was called “Security_Concerns”.
Log Firewall – On (Optional, you do not have to log Firewall traffic but it does help in the beginning. You can always turn it off later.)
Once you have finished, save the rule and test out your systems. Make sure you can access everything you need including everything on your local network such as printers and NAS units. Depending on your particular setup, you may need to tweak some of the settings you just made, or if you are being blocked from accessing a particular resource, you may have to create a bypass rule for that device such as a NAS. It is best to try things out before making any more setting changes. This is all it takes to create a “Basic” rule. Though it appears intimidating, you will find that it is actually fairly straight forward, and making subsequent changes only relies on changing the specific items such as the URL group, Web Filter, or Application Filter. You can adjust these elements as much as you want without having to go ack and adjust the rule itself.
Dynamic DNS
Sophos XG has many extra features that go beyond the typical Firewall. I will not get into all the features, but I do want to cover a couple. The first thing that I found useful was Dynamic DNS. Many of us have providers that periodically update our IP addresses. Nowadays it does not happen nearly as often as 5-10 years ago but it still happens. One great way to work around this issue is to use a DNS service that allows you to use a URL in your mobile applications eliminating the need to always stay current with your IP address in addition to adding a bit of security when you setup your laptop or mobile devices.
Security Dashboard and Custom Reports
Though I was not to impressed with the canned reports, the dashboards and custom reports are really powerful and can be customized to your particular needs.
Summary
Though it may seem a bit overwhelming at first, as you have seen most things do follow a pattern as you break them down into smaller elements. Not to say that they could not make things a bit easier, but the is a logic there. Despite a few flaws, the software is extremely powerful and ratchets down potential security concerns especially if you have others in the house that may not be as security conscious or do not completely understand what to do. For now (hopefully address in the May release) there is one minor flaw and that is that your wireless IOS/Android phones and tablets will have to use an access point that is filtered to avoid getting bypassed if you need stream Netflix to them, but overall this is a wonderful product that will get better overtime. The ease of use once you understand it makes this even more powerful for the average user and still has a strong list of features for the more experienced. On the next round I will try to get more into the VPN and provide an update of changes once they have their new release out in the wild.












[…] https://thedocsworld.net/sophos-xg-firewall-part-2tightening-security/ […]
cialis over counter walmart
20mg cialis dosage – cialis 20 mg cost who is online – female cialis