After reviewing the navigation and finding my way around the new interface, I was ready to explore some of the new features. It makes sense to start with firewall rules as that is one of main reasons for using something like Sophos in the first place. There have been tons of changes in Sophos XG V16 and I will cover some of these changes in future posts, but since the rules are the key to making things work, I will start by covering the changes in the rules section as well as go through some sample setups.
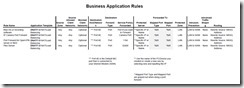
The layout of Sophos XG V16 is quite different and the process of creating a rule is much easier as you can see all the critical information at once without the need to scroll up and down. As before, there are two main types of rules, a business application (port forwarding), and a network/user rule. I will try and cover each with examples and I have also added a sample rules chart at the bottom to help make things a bit easier. These are only guides and are generic, but hopefully this will help simplify your first few rules.
Business Rules
Business rules are most commonly used for creating a port forward. There are many other uses in business, but in the home, the primary use case is port forwarding. This process has been simplified however they have changed things around and you will need to know about templates. Remember also that once you create your first rule, you can use the clone feature to create multiple variation of the rule. For example if you create one rule that forwards a camera and you would like to forward 3 more, you can clone the rule 3 times and just change the destination and port.
When creating a port forward rule you will mainly use the DNAT template in creating your rule. It sounds complicated but as you will see, that is really the only template you will use. Once you select the DNAT template, just type in the “Name”, description, and for now leave the rule position at the top. Like most firewalls, the rules are read from the top down and can be changed at anytime if needed. Port forwarding rules are not very critical so it will not make any difference at this time what the order is.
Next is to define the Source of the rule. In the case of a port forward rule, the source is not critical as you are typically forwarding “Any” zone (LAN, WAN, VPN, Etc,) from any network. You can restrict this as much as you want such as limiting it to the WAN port or from as certain IPs, as well as using the new feature that makes it easier to block certain countries. As you can see from my example, you can block individual countries, or create a group that has a whole list that I can manage without adding each country separately.
The next step is where you are forwarding it to. This has been simplified in the new version and the Destination is typically your WAN port (port #2 by default). The forward type in this example is “Port” (you have a choice of Port, Port Range, Port List, and Everything), and the “Service port(s) Forwarded”. All you need here is the port(s) numbers.
Next is the section where all this being forwarded “To”. Under the “Protected Servers” you will select the destination such as a computer, NAS, etc. In this example, I am forwarding to a QNAP NAS which I assigned a fix IP to. The only other entry you will need is the Zone which again will typically be the LAN in a port forwarding rule as the goal usually is forward an outside port on the WAN to a port and computer on your LAN. Another example would be something like forwarding a port from your WAN to the computer that runs your security cameras so you can access them remotely.
Lastly, you will select the intrusion prevention rule. Here you can use one of the standard ones or create a custom one yourself. I would suggest selecting one of the canned ones such as LAN to WAN. For now, leave the traffic shaping to “None”, Synchronized Security stays off as that is a business feature, and select Masquerading and use the default “MASQ”. There is also the option to log traffic which is helpful at first but my suggestion is to only use it where you need it as it will consume resources and use storage. Use logging for troubleshooting and wait till you have everyting setup the way you want and then decide what you want to track.
Network Rules
This is the area that is the most powerful and contains the capability of controlling everything about your network. This is where you can define very finite controls over all, or part of your network and the ability to lock things down as tight as you want it. We will start with an explanation of how these rules work, and as a reminder there is a list of sample rules at the end of this article which will hopefully get you started. One thing to remember about creating rules is to first break down exactly what you want it to do. For example, if you want to block your family computer from danger, you will define which computer(s), the destination (WAN), the Web/Application filters you want to apply. Once you know this, you will find it easy to create rules.
The first thing you need to know in this section is what you are trying to accomplish. Is the purpose of this rule to allow traffic or block traffic? After creating a name, you must select which action you want (allow, block, or reject). Then enter in a description and define the position of the rule. Again, the position at this point is not important as it can be moved. If you are wanting to connect to the internet, even if heavily filtered, you need to select “Allow”.
Source
The next section you select the “Source Zone” (LAN, WAN, VPN, etc.). Most of the time this will be the LAN. Depending on the purpose of the rule, the next section, “Source Networks and Devices” is very critical to making the rule work the way you want. So, if I want to block or apply special filtering to a specific computer, I would select LAN as the “Source Zone” and the IP address (Computer Name) for the Source Networks and Devices.
Destination
Next is selecting the destination. If you created the original rule to “Block” a specific computer or computers then you would select WAN for the Zone, and ANY for the Destination Network. This would block all internet (WAN) connections from the computer you selected in the “Source”. In contrast, if you selected “Allow” in the first part of the rule, it would allow all traffic to the internet (WAN) from the computer(s) you selected in the “Source”.
Depending on how you setup your users and network (most do not setup up users in a home environment), this last area is typically unchecked and not tied to a user. If you force a log in and create users, you could check the “Match Known Users” and select the user or group this rule would apply to. For me I associate a rule with a specific computer(s) or network so I leave this unchecked. Lastly you can decide whether to log traffic. For rules, this is very useful especially when you are trying to monitor what is going on a computer or network.
Summary
This is obviously just a couple of examples from literally hundreds or thousands of possibilities based on your particular network, but hopefully with the samples I created in the charts below you will begin to see the ease and power that are available to you from Sophos XG V16 for free. I think the original version of XG was great but to large extent it was laid out in a very clumsy way making it seem more complicated than it really was. It is not perfect and there are things that still could be easier such as assigning static IPs, but it has come along way in the right direction. Take a look at the charts below and you will begin to see a pattern to the logic they use and hopefully you will find it as useful and powerful as I have.
Sample Rules
Below are links to a chart for some sample rules. Many of them assume you know how to create Web and Application Filters to suit your needs. If you not sure or if you need a refresher, see my first two articles. It looks allot more complicated than it is.
For additional information, see the following articles. They are from version 15 but much of the information still applies.
https://thedocsworld.net/sophos-xg-firewall-1-the-basics/
https://thedocsworld.net/sophos-xg-firewall-part-2tightening-security/