Sometimes you go along thinking that everything is great, your hardware is working, you have great network security, and you exercise safe computing. So what could possibly go wrong? Turns out a bunch of stuff can go wrong and one day you get that rude awakening that you have taken things for granted and have assumed that you did enough.
Prelude
I have worked hard to create what I thought was a very secure network. I use client level security software, Untangle as my firewall, router level antivirus, and two physical networks to keep things separated and away from danger. I am very, very careful about what and where I access, and my laptop is always connected to a VPN so I do not have to worry about wireless access concerns outside the house. I have given allot of thought and planning to my home network and thought that I had things pretty well locked down. But I was wrong…
So what happened? I will spare you all the details of what lead up to discovering this breach, but it turns out that one of the systems in the house became a victim to some unfriendly software (I believe it was a game) which effectively turned that system into a peer to peer node. Fortunately this was on a separate physical network different than the one I use for my data so network browsing was harder to do. In addition, I do not keep any critical data on any of the clients and passwords are required to access any of the data on the NAS or servers. I was actually notified by my internet provider that I was potentially transmitting data (long story). At first I thought this was not real or possible however after contacting them, I found out it was real. After picking myself off the floor, I began my quest to locate and kill whatever was on my network and kill these services off the affected system. In addition, I was now on a mission to lock my network so this would not happen again. If this has not happened to you I can tell you it definitely works better at jolting your blood pressure that any coffee I ever had.
Application Control to the Rescue
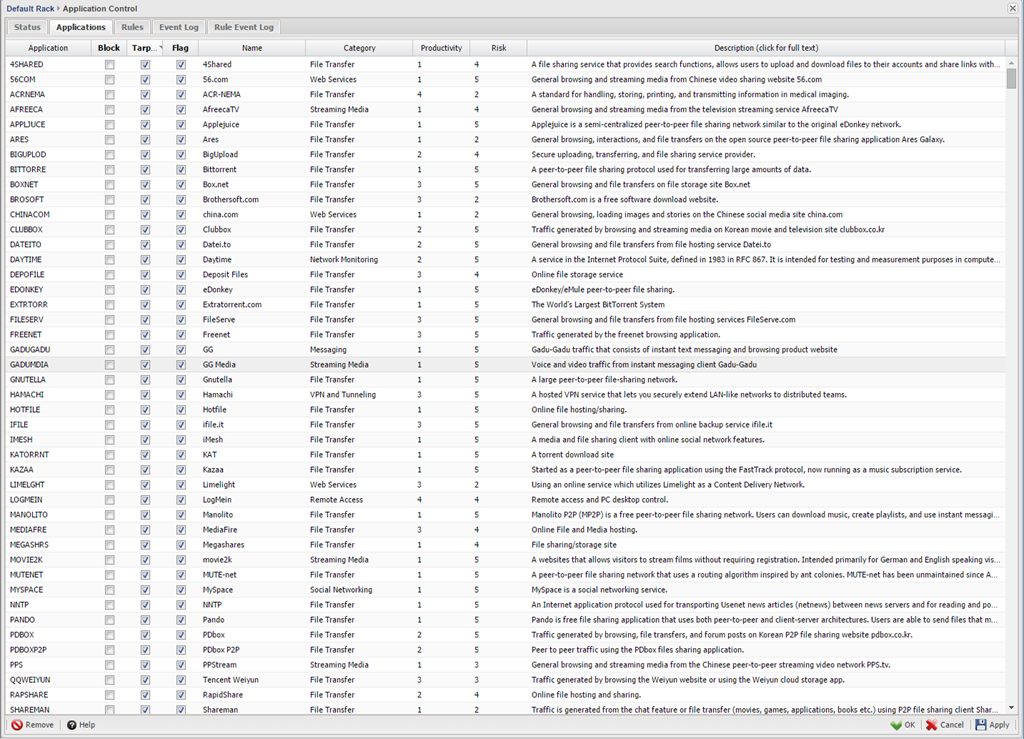
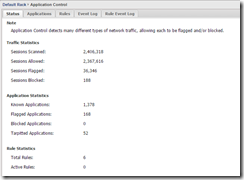
There are numerous ways to solve these kinds of problems but after doing some research and knowing that I wanted a router/server level solution rather than a client level, I looked at the various solutions that the UTM companies had to offer. Since I wanted something that was router/server based so that I could protect all the systems in the house, I ended up deciding to better exploit what I already had, Untangle (NG Firewall as it now known by). I chose this partially for its capabilities and partially because I am already invested in it and everything is already configured so I really did not want start everything over from scratch unless there was a compelling reason to do so. I will also cover some of the native free applications that are built in but in the end I needed a stronger solution than what they offered for free so I bit the bullet and purchased the “Application Control” module which would offer me the application level control over things like peer to peer services. If you look at the picture below, you will see only a very small listing of the hundreds of applications that you have control of.
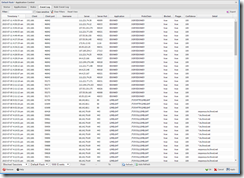
When I initially set it up, I was shocked at looking at the logs. There were things running and installed on these systems that I had no idea was there. Don’t get me wrong, not all was bad, but a surprise none the less.
So what does it do and how does it work? Here is an excerpt from their site that explains better and covers all the key highlights of the module
Translated, this means I would now have the capabilities to protect my network from these types of internal breaches far more than I had before. In addition, one of the features I liked was a feature they call “Tarpitting”. Since many of these apps will reattempt with a different port if they are blocked outright, Tarpitting actually allows them to connect fooling the application into thinking it is properly connected then simply does not allow any data to pass through. Though I have not done enough testing to validate this, it appears to have allot of merit. The downside, $27/Month or $270/year subscription which is a bit steep. Untangle is an industrial strength product that may seem like an overkill, but after suffering the pain of stripping down systems and countless hours of troubleshooting, I was very happy to pay for the peace of mind and the control. Even if any of the systems get infected again by other users in the house, at least things will not be sent out and I can breathe a bit easier knowing data is better protected, and my network has not become a peer to peer node for file sharing. Are things ever 100%? No, but after this experience, I want to tilt the odds in my favor as much as I can. Just a guess, but if it ever happens to you I’m betting you will too. If you look at these pictures, you will see that there are hundreds of attempts to connect externally mostly isolated to two systems in the house. When I examined what was installed on these two systems, I could not detect anything specific that could easily be un-installed except for Hamachi which had been installed on one of the kids systems during a game install. Not seeing specifically where it was coming from is what bothered me the most. If I would have found one item I could nail down as the problem, I would have felt better. Not knowing, or not being able to pin point it was frightening.
Web Filter
In addition to blocks I enabled in the application control, I also activated the Web Filter module. This allowed me to add even more control by category blocking, blocking specific sites that show up on the logs that I do not want anyone visiting.
Moving Data
Though I have not stored data on a local machine in years that was not the case on other systems I found in the house. Even after installing all the protection, I moved all resident data off of these systems to a NAS behind another layer of passwords.
Conclusion
If you would have asked me a few months I would have told you that I have things pretty tight and under control. I have segregated networks, a good firewall, security software, and use as many precautions as I can. If you ask me the same question today I assure you I will give an entire different answer and I now take nothing for granted. The best advice I can give someone now is that you do the same. You can select the solution that works best for you but just make sure you do everything you can to protect yourself.
I know this might seem like a bit of overkill and slightly complex, and a month ago I would have agreed with you, however if you went through what I went through, you might not think that anymore. I not saying this is the only way nor am I saying that it is the best way, but rather this is what I chose and so far it has worked well for me. Sure there was a learning curve, some trial and error, but in the end it seems to provide me the security I need. I can tell you this, I am fairly confident that I will not be taking network security for granted anymore and will be on the constant lookout for better ways to lock things down. If I can leave you with one thought it would be that you do something to enhance your network security and don’t let this be an area where you skimp especially if you have kids, teenagers, or inexperienced users in the house. Even if you are not already infected (which like me you may not know) it is far less painful to spend time and money upfront than it is after it is too late.